my own indieAuth provider!
indiko.dunkirk.sh/docs
indieauth
oauth2-server
docs: fix image link
+7
-1
+7
-1
README.md
+7
-1
README.md
···
1
1
# Indiko
2
2
3
-
3
+

4
4
5
5
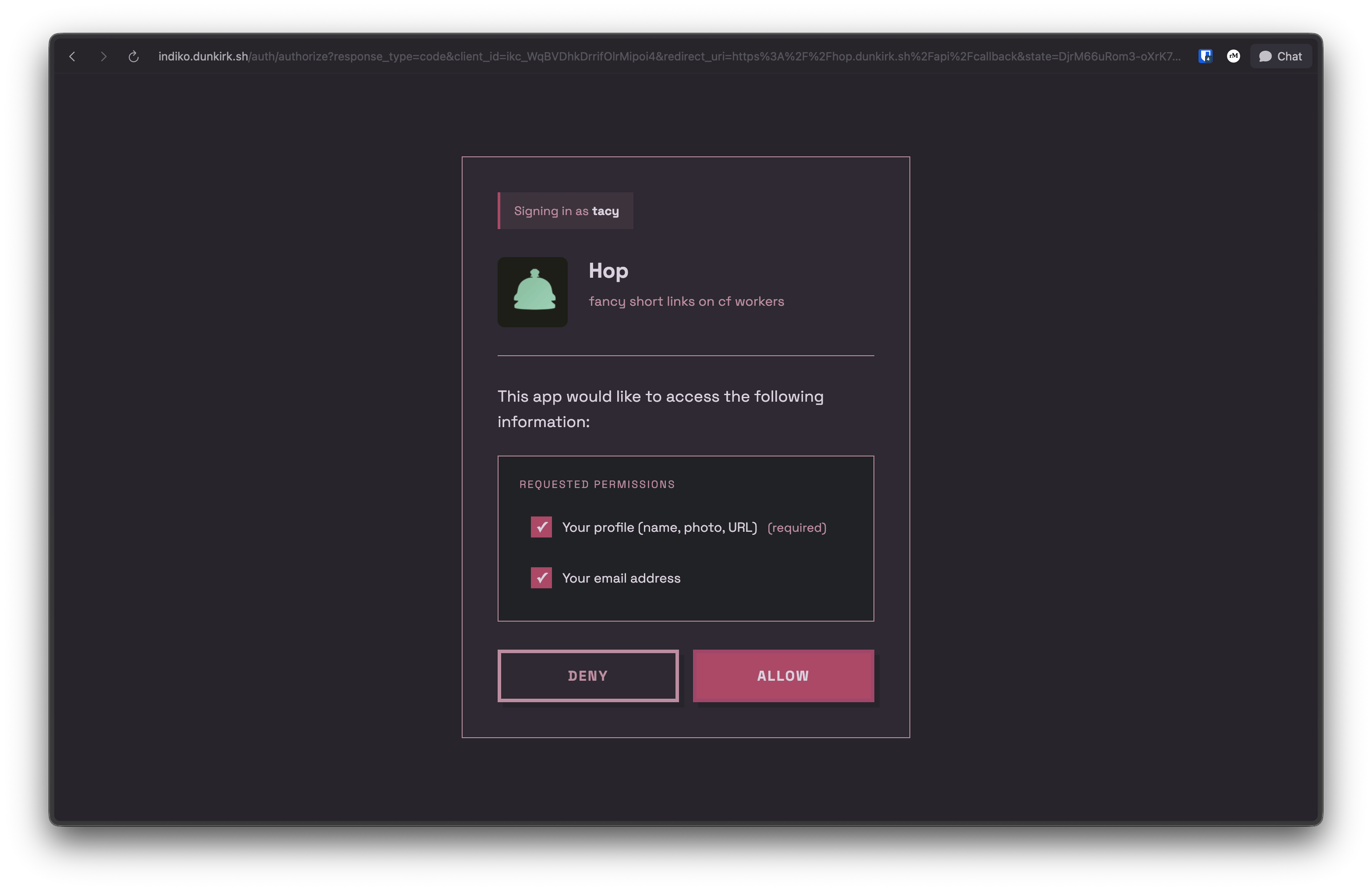
No that was not a typo the project's name actually is `indiko`! This is a small implementation of [IndieAuth](https://indieweb.org/How_to_set_up_web_sign-in_on_your_own_domain) running on bun with sqlite and serving as the authentication provider for my homelab / side projects it also supports custom clients with roles over the OAuth 2.0 spec.
6
6
···
79
79
#### Auto-registered Clients (IndieAuth)
80
80
81
81
Any app can use Indiko without admin approval. On first authorization:
82
+
82
83
- Use any valid URL as your `client_id` (e.g., `https://myapp.example.com`)
83
84
- Indiko fetches metadata from your `client_id` URL
84
85
- App is automatically registered
···
95
96
1. Go to `/admin/clients`
96
97
2. Click "Create OAuth Client"
97
98
3. Fill in:
99
+
98
100
- **Name** - Display name for your app
99
101
- **Logo URL** - (Optional) URL to app logo
100
102
- **Description** - (Optional) Brief description
···
103
105
- **Default Role** - (Optional) Auto-assign this role on first auth
104
106
105
107
4. Save and copy the generated credentials:
108
+
106
109
- **Client ID** - Format: `ikc_xxxxxxxxxxxxxxxxxxxxx`
107
110
- **Client Secret** - Format: `iks_xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx`
108
111
···
110
113
> The client secret is only shown once! Save it securely.
111
114
112
115
**Pre-registered clients:**
116
+
113
117
- **MUST use both PKCE and client_secret** in token requests
114
118
- Support role assignment for RBAC (Role-Based Access Control)
115
119
- Admin-managed metadata and permissions
···
135
139
Indiko also supports OpenID Connect (OIDC) for modern authentication flows:
136
140
137
141
**Discovery endpoint:**
142
+
138
143
```
139
144
https://your-indiko-domain.com/.well-known/openid-configuration
140
145
```
141
146
142
147
**Key features:**
148
+
143
149
- Authorization Code Flow with PKCE
144
150
- ID Token with RS256 signing
145
151
- JWKS endpoint for token verification